Let’s dive into a topic that might give you the chills—cybersecurity skeletons in the closet. You may not have old skeletons hidden away in the basement. But there’s a good chance of cybersecurity vulnerabilities lurking in the shadows, just waiting to wreak havoc.
You can’t fix what you can’t see. It’s time to shine a light on these hidden dangers. So, you can take action to protect your business from potential cyber threats.
Let’s get started uncovering threats that could leave your business in danger. Here are some of the most common cybersecurity issues faced by SMBs.
Outdated Software
We get it; updating software can be a hassle. But running outdated software is like inviting hackers to your virtual Halloween party.
When software vendors release updates, they often include crucial security patches. These patches fix vulnerabilities that hackers can exploit. So, don’t let outdated software haunt your business. Keep everything up to date to ensure your digital fortress is secure.
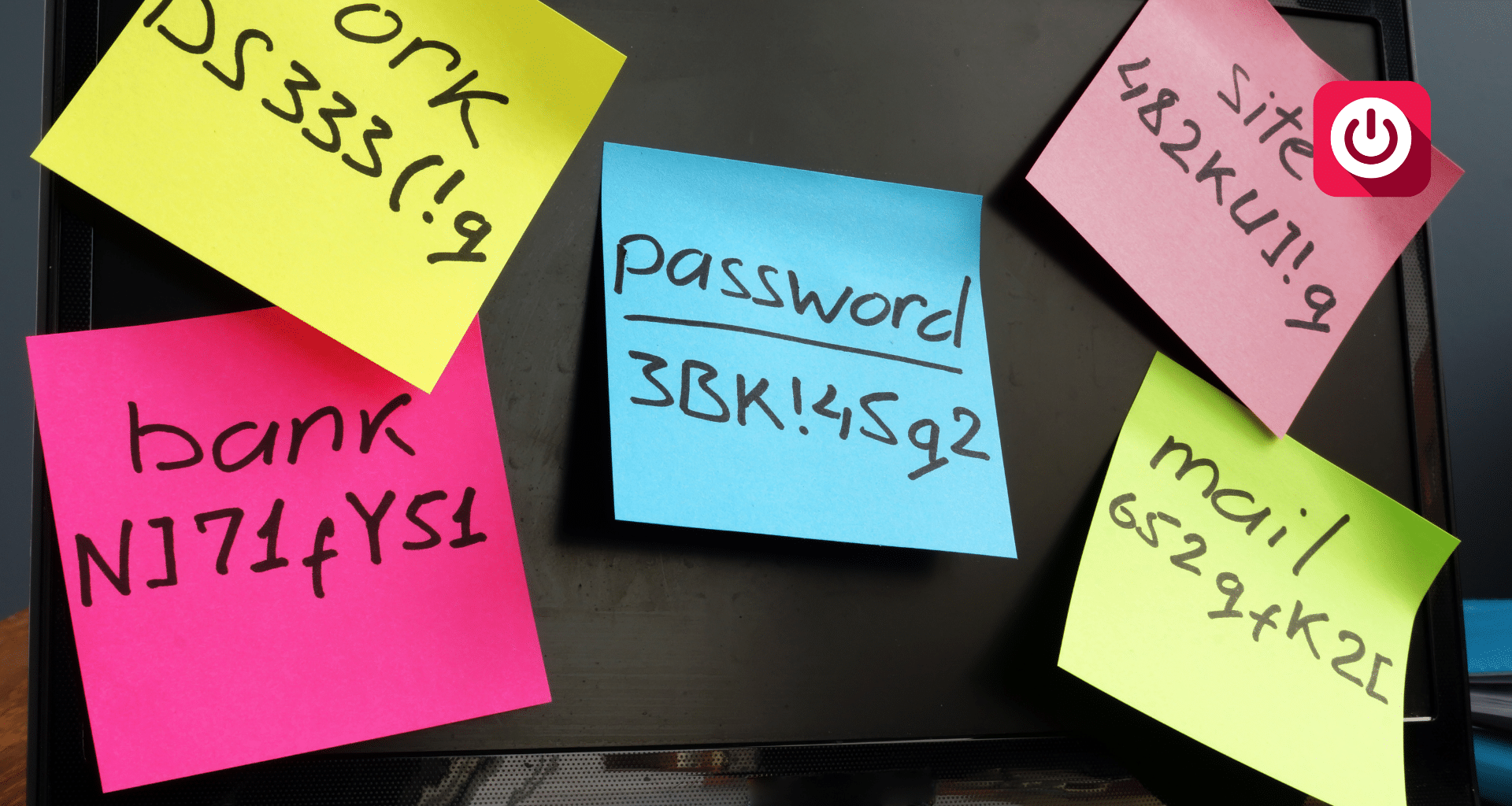
Weak Passwords
If your passwords are weak, you might as well be handing out your office keys to cyber criminals. Using “123456” or “password” as your login credentials is a big no-no.
Instead, create strong and unique passwords for all accounts and devices. Consider using a mix of upper and lowercase letters, numbers, and special characters. Password managers can be a lifesaver for generating and storing complex passwords securely.
As a business owner, you can’t expect your employees to do this naturally. Provide them with requirements for creating passwords. You can also set up software to force strong password creation.
Unsecured Wi-Fi
Picture this: a cybercriminal sitting in a parked car. He’s snooping on your business’s unsecured Wi-Fi network. Scary, right? Unsecured Wi-Fi can be a ghostly gateway for hackers to intercept sensitive data.
Ensure your Wi-Fi is password-protected. Make sure your router uses WPA2 or WPA3 encryption for an added layer of security. For critical business tasks consider a virtual private network (VPN). It can shield your data from prying eyes.
Lack of Employee Training
Your employees can be your business’s strongest line of defence or its weakest link. Employee error is the cause of approximately 88% of all data breaches.
Without proper cybersecurity training, your staff might unknowingly fall victim to phishing scams. Or inadvertently expose sensitive information. Regularly educate your team about cybersecurity best practices.
Such as:
- Recognising phishing emails
- Avoiding suspicious websites
- Using secure file-sharing methods
No Data Backups
Imagine waking up to find your business’s data gone, vanished into the digital abyss. Without backups, this nightmare can become a reality. Data loss can be due to hardware failures or ransomware attacks. As well as many other unforeseen disasters.
Embrace the 3-2-1 rule. Have at least three copies of your data, stored on two different media types. With one copy stored securely offsite. Regularly test your backups to ensure they are functional and reliable.
No Multi-Factor Authentication (MFA)
Using only a password to protect your accounts is asking for trouble. It’s like having nothing but a screen door at the entrance of your business.
Adding MFA provides an extra layer of protection. It requires users to provide extra authentication factors. Such as a one-time code or passkey. This makes it much harder for cyber attackers to breach your accounts.
Disregarding Mobile Security
Mobile devices have become office workhorses. But they can also be haunted by security risks. Ensure that all company-issued devices have passcodes or biometric locks enabled. Consider implementing mobile device management (MDM) solutions. These will enable you to enforce security policies. As well as remotely wipe data and ensure devices stay up to date.
Shadow IT
Shadow IT refers to the use of unauthorised applications within your business. It might seem harmless when employees use convenient tools they find online. But these unvetted applications can pose serious security risks.
Put in place a clear policy for the use of software and services within your business. Regularly audit your systems to uncover any shadow IT lurking under cover.
Incident Response Plan
Even with all precautions in place, security incidents can still happen. Without an incident response plan, an attack can leave your business scrambling.
Develop a comprehensive incident response plan. It should outline key items. Such as how your team will detect, respond to, and recover from security incidents. Regularly test and update the plan to ensure its effectiveness.
Need Some “Threat Busters” to Improve Your Cybersecurity?
Don’t let cybersecurity skeletons in the closet haunt your business. We can help you find and fix potential vulnerabilities. As well as create a robust security posture that protects your business.
Give us a call today to schedule a cybersecurity assessment.