Effortless IT Support Tailored for Businesses in St Albans and Beyond Experience proactive, reliable IT solutions designed to keep your business running smoothly while you focus on growth.
For over 13 years, we have been providing IT support to business owners in St Albans and the surrounding towns and counties. Our mission is to truly understand your business and become a trusted partner, not just another IT provider. We deliver comprehensive IT support that simplifies the complex, offering straightforward and proactive IT solutions to help small and medium-sized businesses operate with confidence. We specialise in helping businesses maximise the potential of their technology while ensuring their IT systems are secure and reliable. Let us handle your IT challenges, so you can focus on what you do best.
What our Customers are saying…
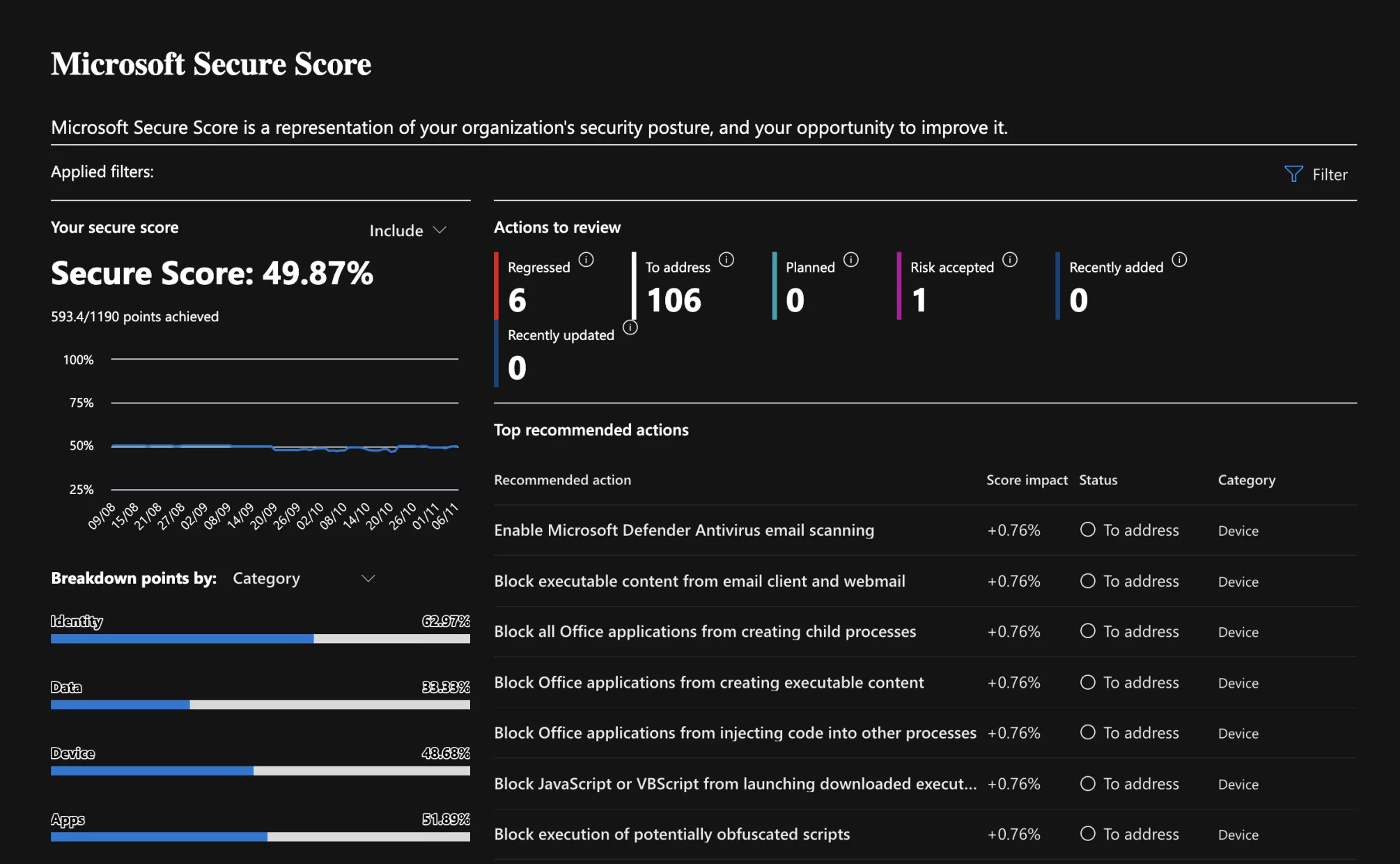
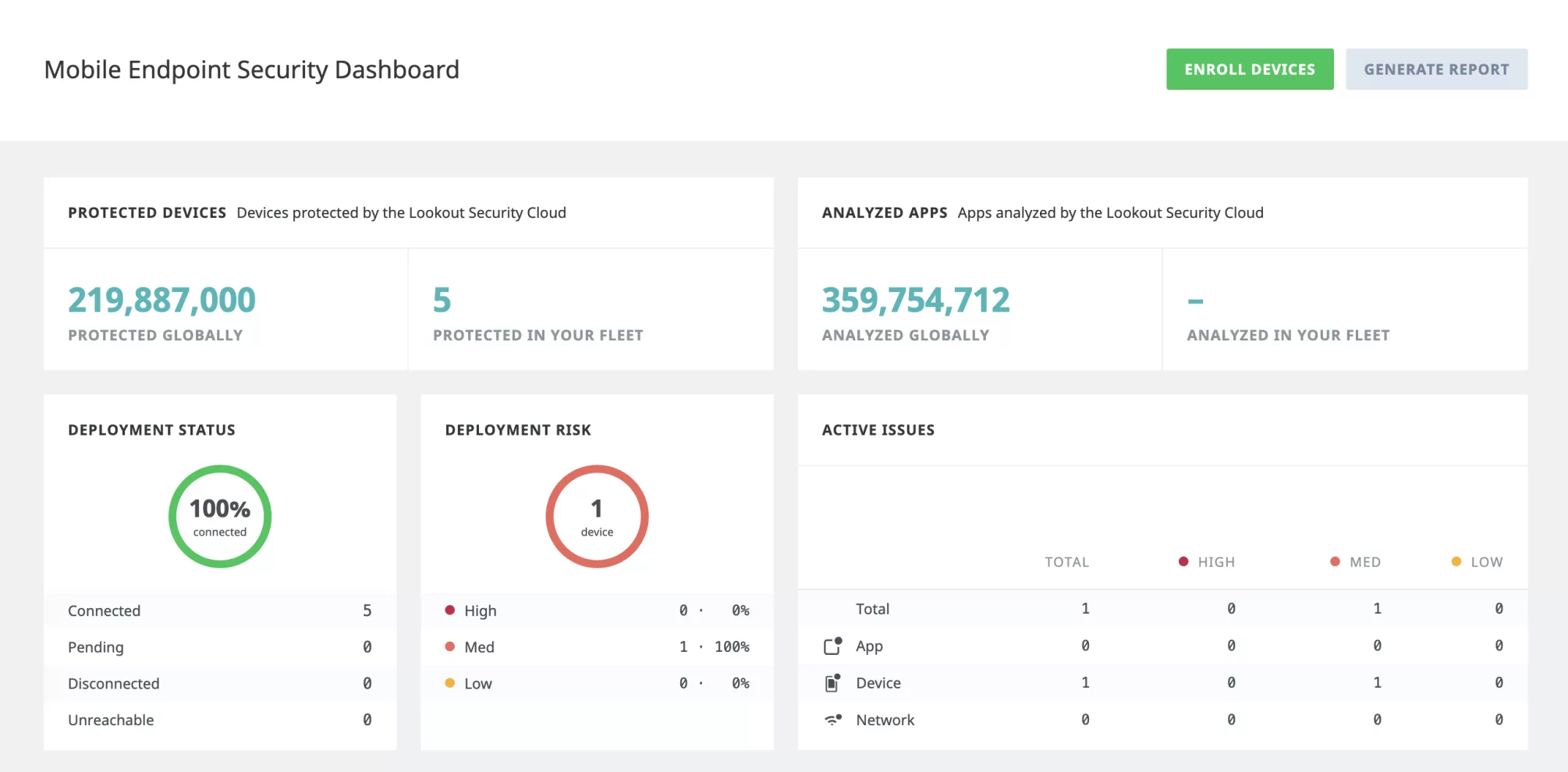
Protect Your Business
In today’s digital age, cyber threats are constantly evolving and becoming more sophisticated. It’s crucial to stay one step ahead to protect your business from potential attacks. Our comprehensive IT security services are designed to provide you with the peace of mind you need.
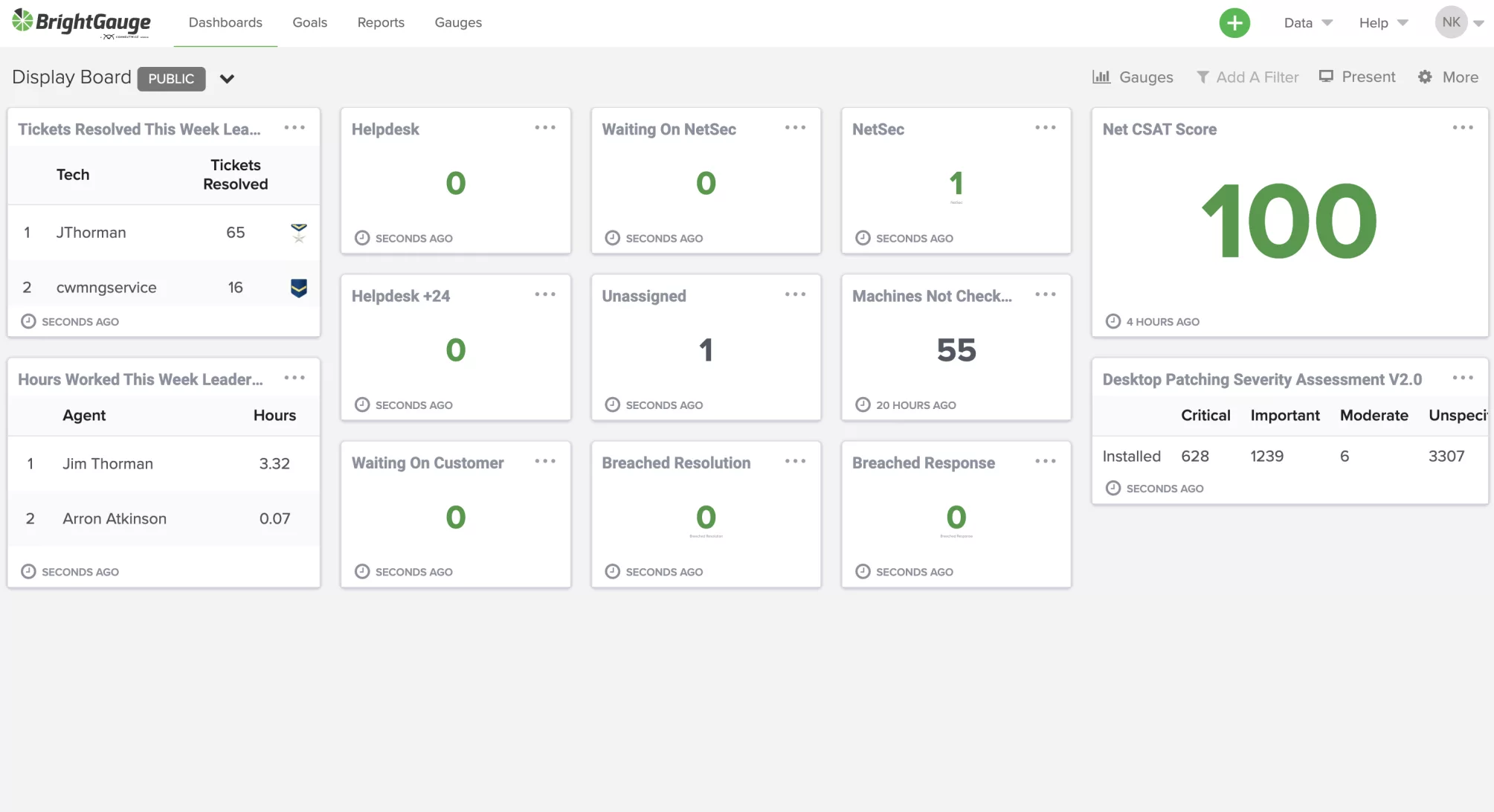
Stay One Step Ahead with 24/7 Cyber Security and IT Support. In an era where cyber threats are lurking around every corner, our managed IT security services act as your vigilant defender, safeguarding your business with round-the-clock surveillance1.
Our state-of-the-art Security Operations Centre works tirelessly to ensure your computers and data are shielded from evolving cybercrime threats. With our advanced monitoring and proactive threat detection, we can identify and mitigate risks before they become serious issues.
Outsource with Confidence Friendly Skilled Technicians
Friendly and Skilled Technicians. Access a wealth of knowledge and industry experience that’s hard to match in-house. Our team is up-to-date with the latest tech innovations to streamline and secure your business operations3.
By outsourcing your IT security to us, you can focus on what you do best – running your business. Our friendly and skilled technicians are always ready to assist you, providing expert support and guidance whenever you need it.

RESOURCES

Check Your Email Address
Use our tool and check to see whether your email has been breached at any time, and what company had the breach

Does Your Email Authenticate
Having issues with emails not reaching the recipients, use our DMARC tool to see if you have it added to your domain

How much could you lose ?
Your business could potentially lose thousands in as little as 5 hours of downtime

How much can we save you ?
See your potential savings by ensuring your protected from viruses and malware & make sure your backups are running
reach out to us and see how we can help
Talk to us
Take the Stress Out of IT Management Today Let us handle the tech, while you focus on what you do best.
Secure your business’s future with our cutting-edge IT Security Services.
Get Started with Managed IT Security Services Today! Secure your business and ensure peace of mind.